Biometric Hardware Wallets_ The Next Step in Physical Security_1
In the ever-evolving landscape of digital security, one innovation is standing out: biometric hardware wallets. These cutting-edge devices are not just the next step in physical security; they're a paradigm shift in how we safeguard our digital assets. As we dive into this fascinating world, we'll explore the intricate blend of biometric technology and hardware wallet design, revealing how these devices are redefining security in an increasingly digital world.
The Evolution of Security
Security has always been a cornerstone of digital transactions, from simple passwords to complex two-factor authentication systems. However, traditional security measures often fall short in the face of evolving cyber threats. Enter biometric hardware wallets, the latest innovation in physical security.
Biometric Technology: Beyond Passwords
Biometrics, the use of unique biological traits to verify identity, has been around for some time. Fingerprints, facial recognition, and even iris scans have become familiar features in our daily lives, particularly in mobile devices. But what makes biometric hardware wallets a leap forward is their integration into hardware wallets designed for cryptocurrencies and other digital assets.
The Hardware Wallet Revolution
Hardware wallets have long been considered the gold standard for securing digital currencies. These devices store private keys offline, protecting them from online hacking attempts. Biometric hardware wallets take this concept to the next level by incorporating biometric sensors into the hardware wallet design. This means that instead of relying on a password or PIN, users authenticate their identity using a unique biological trait.
Convenience Meets Security
One of the most significant advantages of biometric hardware wallets is the seamless blend of convenience and security. Imagine unlocking your wallet with a simple touch of your finger or a glance at your face – it’s not just sci-fi; it’s here and it’s secure. This level of ease makes managing digital assets far less daunting, especially for those who may find traditional security measures cumbersome.
Advanced Encryption
Biometric hardware wallets don’t just rely on biometrics for security; they also employ advanced encryption techniques. These wallets use state-of-the-art encryption protocols to safeguard private keys. When combined with biometric authentication, the security is multilayered and virtually impenetrable.
Real-World Applications
Biometric hardware wallets are not just a theoretical concept; they have real-world applications that are transforming the way we handle digital assets. Here are a few examples:
Cryptocurrency Transactions
For cryptocurrency enthusiasts, biometric hardware wallets offer unparalleled security. These devices ensure that your private keys remain offline, protecting your assets from online hacks. With biometric authentication, you can confidently execute transactions, knowing that your identity is also secure.
Digital Identity
Beyond cryptocurrencies, biometric hardware wallets are poised to revolutionize digital identity management. They provide a secure way to store and access sensitive information, reducing the risk of identity theft. This has significant implications for sectors like banking, healthcare, and more.
Enterprise Security
In the corporate world, where sensitive data is constantly at risk, biometric hardware wallets offer a robust security solution. Companies can implement these devices to protect critical information, ensuring that only authorized personnel can access sensitive data.
The Future of Biometric Security
The future of biometric security is incredibly promising. As technology continues to advance, we can expect even more sophisticated biometric systems. Imagine a world where not only fingerprints and facial recognition are used but also other biometric traits like voice recognition and even DNA scanning.
Addressing Concerns
Of course, no technology is without its concerns, and biometric hardware wallets are no exception. Privacy and data security are paramount. However, these devices are designed with the highest standards of security in mind. Biometric data is typically encrypted and stored securely, minimizing the risk of exposure.
Conclusion
Biometric hardware wallets represent a significant leap forward in physical security. By combining the robustness of hardware wallets with the convenience of biometric technology, they offer a future-proof solution for safeguarding digital assets. As we continue to navigate an increasingly digital world, these devices will play a crucial role in ensuring our security and peace of mind.
Stay tuned for part 2, where we'll delve deeper into the technical aspects, specific products on the market, and the potential future developments in this exciting field of biometric hardware security.
Technical Marvels: The Inner Workings of Biometric Hardware Wallets
Having explored the revolutionary impact of biometric hardware wallets on physical security, it’s time to take a closer look at the technical marvels that make these devices so effective. This part will dive into the intricate design, cutting-edge technology, and specific products that are leading the charge in this new era of digital security.
The Technical Core
At the heart of a biometric hardware wallet is the biometric sensor. This component is the key to unlocking the device's advanced security features. There are several types of biometric sensors, each with its own advantages:
Fingerprint Sensors
Fingerprint sensors are among the most common biometric sensors used in hardware wallets. These sensors are incredibly accurate and can differentiate between even the slightest variations in fingerprints. They provide a reliable method of authentication and are relatively easy to use.
Facial Recognition
Facial recognition technology has made significant strides in recent years. Biometric hardware wallets equipped with facial recognition sensors can scan and authenticate users based on their facial features. This method is not only secure but also incredibly convenient, especially in environments where a quick and easy authentication process is essential.
Iris Scanners
Iris scanners are highly sophisticated biometric sensors that authenticate users based on the unique patterns in their irises. These sensors are incredibly secure and difficult to replicate, making them an excellent choice for high-security applications.
Integration with Hardware Wallets
Integrating biometric sensors into hardware wallets involves more than just adding a sensor to the device. It requires a seamless blend of hardware and software to ensure that the biometric authentication process is both secure and user-friendly. Here’s how it works:
Hardware Design
The hardware design of a biometric hardware wallet is meticulously crafted to house the biometric sensor securely. The sensor is often encased in a protective layer to prevent tampering and ensure durability. The overall design also focuses on user convenience, with intuitive interfaces and ergonomic features.
Software Integration
The software component plays a crucial role in the integration of biometric sensors. Advanced algorithms are used to process biometric data and authenticate users. The software must be capable of handling the vast amounts of data generated by biometric sensors and ensuring that it is securely stored and transmitted.
Encryption Protocols
Biometric hardware wallets employ advanced encryption protocols to protect sensitive data. These protocols ensure that private keys and other critical information remain secure, even when the wallet is connected to the internet. Here are some of the encryption methods commonly used:
AES Encryption
Advanced Encryption Standard (AES) is a widely used encryption method known for its robustness. It is particularly effective in securing data stored on hardware wallets and during data transmission.
RSA Encryption
Rivest-Shamir-Adleman (RSA) encryption is another powerful method used in biometric hardware wallets. RSA is known for its security and is often used in conjunction with other encryption protocols to provide an additional layer of protection.
Leading Products on the Market
Several companies are leading the charge in the development of biometric hardware wallets. Here are a few noteworthy products that are setting the standard for this new technology:
Ledger Nano X
The Ledger Nano X is one of the most advanced biometric hardware wallets on the market. It features a built-in biometric sensor, allowing users to authenticate their identity using their fingerprint or facial recognition. The device also has a color screen and Bluetooth connectivity, providing a user-friendly interface and enhanced security.
Trezor Model T
Trezor Model T is another top-tier biometric hardware wallet. It incorporates a high-precision fingerprint sensor and offers a range of security features, including PIN protection and two-factor authentication. The device is known for its durability and robust design.
KeepKey Touch
KeepKey Touch is a biometric hardware wallet that combines a traditional hardware wallet design with biometric authentication. It features a fingerprint sensor and is compatible with a wide range of cryptocurrencies. The device is praised for its user-friendly interface and strong security features.
Future Developments
The future of biometric hardware wallets holds immense potential. As technology continues to advance, we can expect even more sophisticated biometric systems. Here are some potential future developments:
Multi-Factor Authentication
Combining biometric authentication with other security measures, such as PIN codes and two-factor authentication, could provide an even higher level of security. This multi-factor approach ensures that even if one form of authentication is compromised, the others remain secure.
Enhanced Biometric Sensors
Advancements in biometric sensor technology could lead to even more accurate and secure authentication methods. For example, future devices might incorporate voice recognition or even DNA scanning, offering unprecedented levels of security.
Integration with IoT
The integration of biometric hardware wallets with Internet of Things (IoT) devices could open up new possibilities for secure authentication in smart homes and other IoT environments. This could provide a seamless and secure way to manage and access smart devices.
Addressing Challenges
While biometric hardware wallets offer significant advantages, there are still challenges to overcome. Privacy concerns remain a significant issue, as does the potential for biometric data to被滥用或泄露。
制造商和开发者正在采取措施来解决这些问题,包括使用高级加密技术和严格的隐私政策来保护用户的数据。
用户体验和便利性
直观界面设计
设计直观的用户界面,使得用户能够轻松地导航和使用设备。清晰的指示和简洁的菜单可以帮助用户更快地适应新技术。
快速响应
生物识别技术应该能够快速响应,以确保用户在执行交易或访问敏感信息时不会感到等待。这是通过高效的软件算法和先进的硬件实现的。
多重安全层
通过结合生物识别和传统安全措施(如PIN码或密码),可以提供多重安全层,这不仅增强了安全性,还使得系统在某些情况下更加灵活。
市场前景和商业应用
生物识别硬件钱包的市场前景广阔,特别是在数字货币和加密资产管理领域。它也有潜力应用于其他领域,如个人信息保护、企业数据安全、智能家居管理等。
数字货币和加密资产
这是目前最热门和最成熟的应用领域。生物识别硬件钱包为数字货币持有者提供了一个高度安全的存储和交易环境,减少了被黑客攻击和在线平台被攻破的风险。
企业级应用
企业可以使用生物识别硬件钱包来保护其敏感数据和机密信息。这对于需要高度安全性的行业,如金融服务、医疗保健和政府机构尤为重要。
智能家居
在智能家居环境中,生物识别技术可以用于安全地控制家庭设备,如门锁、照明和安防系统。这不仅提升了安全性,还提供了更高的用户体验。
法规和隐私问题
随着生物识别技术的广泛应用,法律和隐私问题也变得越来越重要。各国政府和监管机构正在制定相关法规,以确保这些技术的使用符合隐私保护和数据安全的标准。
隐私保护
生物识别数据是高度敏感的信息,滥用或泄露可能会对个人造成严重后果。因此,必须采取严格的措施来保护这些数据,包括使用高级加密和安全协议。
法律合规
各国对生物识别技术的监管政策不同,企业必须确保其产品和服务符合当地的法律和法规。这包括对数据收集、存储和使用的透明度,以及用户知情同意的要求。
结论
生物识别硬件钱包代表了物理安全的一个重要进步,特别是在数字货币和加密资产管理方面。虽然它们面临着一些技术和法律挑战,但通过持续的技术创新和严格的安全措施,这些挑战是可以克服的。随着技术的不断进步和应用范围的扩展,生物识别硬件钱包有望在未来扮演更加重要的角色。
In an era where the unexpected often takes center stage, "Black Swan Risks 2026" serves as a compelling lens through which we can view the potential upheavals and breakthroughs that lie ahead. Coined by Nassim Nicholas Taleb, "Black Swan" events refer to rare, unpredictable occurrences with significant, often catastrophic, impacts. As we peer into the horizon, the potential for such events to reshape our world is both thrilling and daunting.
The Nature of Black Swan Risks
Black Swan Risks in 2026 aren't just about the cataclysmic; they encompass a spectrum of possibilities—from technological revolutions to geopolitical upheavals. The essence of these risks lies in their unpredictability and their capacity to alter the course of human affairs in profound ways. Understanding these risks requires a blend of foresight, creativity, and an openness to the unknown.
Technological Disruptions
One of the most compelling realms of potential Black Swan Risks is technology. The advent of artificial intelligence, quantum computing, and biotechnology could redefine industries and societal structures. Imagine a world where AI-driven robots seamlessly integrate into daily life, reshaping everything from manufacturing to healthcare. These advancements could create efficiencies unimaginable today, but they also pose risks—job displacement, ethical dilemmas, and cybersecurity threats.
The rapid pace of technological development often outstrips regulatory frameworks, leading to unforeseen consequences. For example, the widespread adoption of facial recognition technology has sparked debates about privacy and surveillance, illustrating the dual-edged nature of technological progress.
Geopolitical Shifts
The geopolitical landscape is another fertile ground for Black Swan Risks. International relations are complex and fraught with uncertainties. A sudden shift in power dynamics, such as a major geopolitical realignment or an unforeseen conflict, could dramatically alter global stability.
Consider the rise of new economic powers and the potential realignment of trade routes. This could lead to a reshuffling of global alliances, impacting everything from international trade to cultural exchanges. The potential for unexpected events—such as a pandemic-induced global recession or a sudden political revolution—underscores the importance of vigilance and adaptability.
Environmental Cataclysms
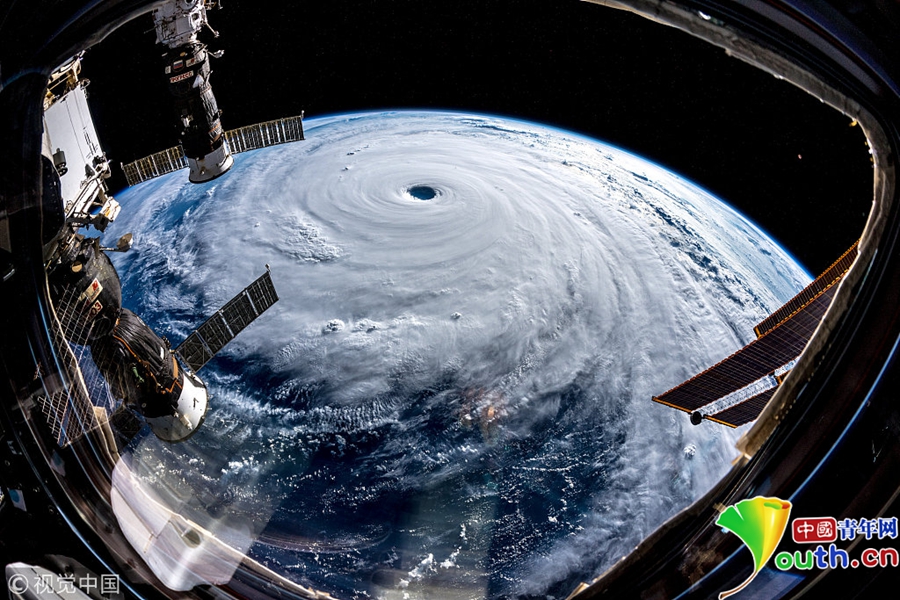
Environmental risks are perhaps one of the most universally acknowledged Black Swan Risks. Climate change, with its myriad unpredictable variables, poses significant threats. Natural disasters, such as hurricanes, earthquakes, and wildfires, could become more frequent and intense, leading to unprecedented human and economic costs.
The potential for a sudden environmental collapse, such as a catastrophic failure of the polar ice caps or a major volcanic eruption, could have far-reaching impacts on agriculture, water supply, and global weather patterns. These events could trigger mass migrations, resource wars, and societal upheaval, highlighting the delicate balance of our planet's ecosystems.
Societal Transformations
Societal changes driven by cultural shifts, social movements, and evolving human values also fall under the umbrella of Black Swan Risks. The way we perceive and interact with each other is continually evolving, influenced by factors such as digital communication, social media, and global interconnectedness.
Movements advocating for social justice, environmental sustainability, and digital privacy could gain unprecedented momentum, leading to sweeping changes in laws, policies, and cultural norms. The rise of global consciousness could foster unprecedented solidarity, but it could also lead to tensions as differing values clash.
Strategic Foresight
In navigating these uncharted waters, strategic foresight becomes a crucial tool. Organizations and individuals must cultivate the ability to anticipate, adapt, and thrive amidst uncertainty. This involves a combination of scenario planning, risk assessment, and agile decision-making.
Scenario planning allows us to explore multiple futures, identifying potential Black Swan Risks and developing contingency plans. By considering various "what if" scenarios, we can better prepare for the unexpected, ensuring resilience and flexibility in the face of change.
Conclusion
As we stand on the precipice of 2026, the potential for Black Swan Risks is both a challenge and an opportunity. The unpredictability of these events demands a proactive approach, one that embraces uncertainty and fosters innovation. By staying attuned to the potential upheavals and breakthroughs that lie ahead, we can better navigate the uncharted waters of tomorrow.
In the next part, we'll delve deeper into specific Black Swan Risks, exploring their potential impacts and strategies for mitigation. Stay tuned for a comprehensive look at the unforeseen forces that could shape our future.
Specific Black Swan Risks in 2026: Potential Impacts and Mitigation Strategies
In the previous part, we explored the broad landscape of Black Swan Risks that could redefine our world by 2026. Now, let's zoom in on specific areas where these risks are most likely to manifest, examining their potential impacts and strategies for mitigation.
Cybersecurity Threats
As we increasingly rely on digital systems, the risk of unprecedented cyber attacks grows. A major cyber event, such as a large-scale data breach or a disruption of critical infrastructure, could have catastrophic consequences. Imagine a scenario where a nation's power grid is hacked, plunging cities into darkness and causing widespread panic.
Impacts:
Disruption of essential services Economic losses Erosion of public trust in digital systems Escalation of international tensions
Mitigation Strategies:
Robust cybersecurity frameworks Regular security audits and updates International collaboration to address cyber threats Development of advanced threat detection technologies
Pandemics and Health Crises
The COVID-19 pandemic has highlighted the vulnerability of global health systems to unexpected outbreaks. A new pandemic, particularly one with a higher mortality rate or more severe symptoms, could overwhelm healthcare systems and disrupt global economies.
Impacts:
Widespread illness and mortality Economic downturns Disruption of global supply chains Social unrest and panic
Mitigation Strategies:
Investment in global health infrastructure Development of rapid response teams Research into antiviral treatments and vaccines Public health education campaigns
Economic Collapses
The possibility of a sudden economic collapse, driven by factors such as a major financial crisis or a global recession, remains a significant risk. Such an event could lead to mass unemployment, social unrest, and political instability.
Impacts:
Widespread poverty and inequality Political upheaval Increased crime rates Migration crises
Mitigation Strategies:
Diversification of economies Implementation of progressive taxation Social safety nets to support the unemployed International economic cooperation
Technological Overreach
The rapid advancement of technology, particularly in areas like AI and biotechnology, could lead to unforeseen consequences if not carefully managed. For example, unchecked AI development could lead to autonomous systems that operate beyond human control, posing existential risks.
Impacts:
Loss of human control over advanced technologies Ethical dilemmas Potential for misuse Social displacement
Mitigation Strategies:
Ethical guidelines for technological development Regulatory oversight Public engagement in policy-making Investment in human-centered technologies
Environmental Disasters
The potential for sudden environmental disasters, such as massive volcanic eruptions or the collapse of major ecosystems, remains a looming threat. These events could have devastating effects on human populations and global ecosystems.
Impacts:
Loss of life and displacement Environmental degradation Economic disruption Global climate change acceleration
Mitigation Strategies:
Climate change mitigation efforts Investment in renewable energy Conservation of natural habitats Disaster preparedness and response planning
Geopolitical Upheaval
Geopolitical tensions, such as sudden conflicts or the rise of new global powers, could lead to significant shifts in international relations and global stability.
Impacts:
Escalation of international conflicts Disruption of global trade Refugee crises Political instability
Mitigation Strategies:
Diplomatic engagement and conflict resolution Economic incentives for peace Humanitarian aid and support for displaced populations International peacekeeping efforts
Cultural and Social Shifts
The rapid evolution of cultural and social norms, driven by factors such as globalization, social media, and demographic changes, could lead to unexpected societal transformations.
Impacts:
Cultural clashes and tensions Changes in social behaviors and norms Polarization of societies Emergence of new social movements
Mitigation Strategies:
Promotion of intercultural dialogue Support for inclusive policies Education and awareness campaigns Encouragement of civic engagement
Conclusion
As we navigate the intricate web of Black Swan Risks, the importance of strategic foresight, resilience, and adaptability cannot be overstated. By anticipating potential upheavals and developing robust mitigation strategies, we can better prepare for the unforeseen and harness the opportunities that lie ahead.
In a world where the unexpected is not just possible but probable, embracing uncertainty with creativity and foresight will be key to thriving in the uncharted waters of tomorrow. Stay tuned for more insights on how to navigate the future with confidence and agility.
NFT RWA Hybrid Plays 2026_ Exploring the Future of Digital Ownership
The Integration of AI Pilots and Web3 Settlement in Autonomous Drones_ Pioneering the Future